-
January 29th, 2022, 08:46 AM
#1
 Create New Cert for AntiSpam Server
Create New Cert for AntiSpam Server
Generate new set from below and paste info to server's web console and then REBOOT for changes to take effect. If you use the renew method, you only need to copy the certificate and not the private key. The keys and certs are located at /etc/postfix/certs. Postfix uses the master.cf for settings.
- openssl genrsa -out new.key
- openssl req -new -key new.key -out new.csr
- openssl x509 -req -days 3650 -in new.csr -signkey new.key -out new.cert
Last edited by glen; May 2nd, 2024 at 08:45 PM.
Let's Dance, Punk.
-
May 15th, 2022, 10:07 PM
#2

Only do this method if you want new private key every time. Copy and Paste:
openssl req \
-x509 \
-newkey rsa:2048 \
-sha256 \
-days 3650 \
-nodes \
-keyout new.key \
-out new.crt \
-subj '/CN=spam.nguy.ca' \
-extensions san \
-config <( \
echo '[req]'; \
echo 'distinguished_name=req'; \
echo '[san]'; \
echo 'subjectAltName=DNS:localhost, DNS:*.nguy.ca, IP:192.168.10.5, IP:192.168.10.6, IP:192.168.10.7')
To verify:
openssl x509 -in new.crt -text -noout
Last edited by glen; May 2nd, 2024 at 08:44 PM.
Let's Dance, Punk.
-
May 2nd, 2024, 01:17 PM
#3

Renew certificate with existing private key:
Create CSR and Convert to CRT:
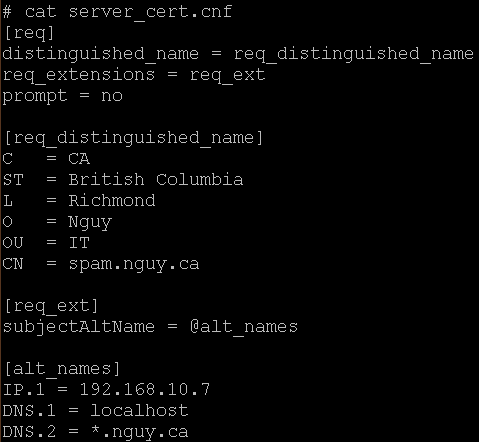
- openssl req -new -key scrollout.key -out new2024.csr <== run this first if "server-cert.cnf" file has been modifed
- openssl x509 -req -days 3650 -in new2024.csr -signkey scrollout.key -out new2024.crt -extensions req_ext -extfile server-cert.cnf <== renew with this line
Add the new certificate to your "Trusted Root Authorities | Certificates " sub folder and delete the old one.
Last edited by glen; May 12th, 2024 at 07:55 PM.
Let's Dance, Punk.
 Posting Permissions
Posting Permissions
- You may not post new threads
- You may not post replies
- You may not post attachments
- You may not edit your posts
-
Forum Rules






 Reply With Quote
Reply With Quote